Why Tabletop Exercises Became Non-Negotiable
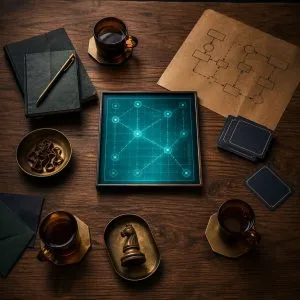
A digital forensics and incident response (DFIR) tabletop exercise is a facilitated, discussion-based simulation of a cyber incident. No computers are attacked. No systems are touched. A facilitator walks the leadership team through a realistic scenario, forcing them to decide — in real time, under time pressure — what they would actually do.
Two developments make this mandatory hygiene for Algerian organizations in 2026.
First, regulatory posture. CISA now publishes Tabletop Exercise Packages (CTEPs) that any organization can use for free, and the UK NCSC's Exercise in a Box provides sector-tailored templates. The Counter Ransomware Initiative, which Algeria tracks through its participation in international cybersecurity forums, published an after-action report making tabletops a baseline expectation across member jurisdictions.
Second, insurance and audit. Cyber-insurance underwriters now ask whether the insured has run a tabletop in the last 12 months. Regulators mandating cybersecurity units under Algeria's Presidential Decree 26-07 will, realistically, soon ask the same question.
The good news: a well-run tabletop costs a room, a facilitator, and two hours. There is no tooling gap.
The Two-Hour Scenario: "Qilin Has Posted You on Their Leak Site"
This scenario is designed for an Algerian bank, telecom, ministry, or mid-sized enterprise. It is realistic because Qilin and DragonForce currently dominate global ransomware activity, per Ransom-DB weekly trend reports. Swap in a different operator if your threat intel team prefers.
Participants (8–12 people): CEO, COO, CISO, IT infrastructure lead, legal counsel, head of communications, head of HR, head of finance, customer support lead, and an optional external observer (MSSP partner, auditor, board member).
Facilitator: a single person outside the direct reporting chain of the CEO — ideally the CISO or an external consultant. They drive the clock and introduce injects.
Time budget: 15 minutes setup, 90 minutes scenario, 15 minutes debrief. Total: two hours.
Scenario opening (T+0)
It is 08:15 on a Monday. The SOC on-call receives an email from a journalist asking for comment on "the security incident at your organization." Attached is a screenshot of your company logo on the Qilin leak-site countdown, claiming 400 GB of data will be published in 72 hours.
Facilitator: "What do you do in the first 30 minutes?"
Expected decisions: activate incident response, call the CEO, contact legal, decide whether to alert the SOC MSSP, decide whether to take external-facing systems offline.
Inject 1 — T+20 minutes
The IT infrastructure lead confirms: three domain controllers are unreachable. Backups on the primary Veeam repository are encrypted. The offsite backup, cloud-based, appears intact but has not been tested in four months.
Facilitator: "Can you restore? How long? Do you trust the offsite? Who authorizes restoring over the production environment?"
Inject 2 — T+40 minutes
A customer-support flood starts: customers report their login credentials are being used to access accounts. The SOC confirms credentials were exfiltrated before the encryption phase.
Facilitator: "Do you force a password reset for all customers? When? Who communicates it? Do you involve ARPCE or the data-protection authority under the Algerian personal data protection framework?"
Inject 3 — T+60 minutes
The Qilin operator contacts the CEO's public email with a ransom demand: 3 million USD, 48 hours, with a proof-of-life sample of 2 GB of sensitive customer data already published on a Tor site.
Facilitator: "Do you engage? Who makes the pay/no-pay decision? Is there a policy? What is legal counsel's position? Are there international sanctions implications?"
Inject 4 — T+80 minutes
A journalist from El Watan and a TSA reporter publish stories based on the leaked sample. Social media lights up. A screenshot of an internal email is circulating on Twitter.
Facilitator: "Who speaks? What do you say? Do you issue a formal statement? Do you brief the minister? Do you activate crisis communications?"
Debrief — T+90 to T+105 minutes
Every participant answers three questions in turn: "What worked?" "What did not work?" "What is the single most important thing we need to fix before the next tabletop?" The facilitator captures these verbatim.
What a Good After-Action Report Looks Like
The facilitator produces a one-page after-action report within 48 hours. It has exactly three sections.
- Confirmed capabilities. Things the organization would clearly do correctly — for example, "IT has a tested process to revoke all Active Directory credentials in under 30 minutes."
- Identified gaps. Things the organization could not answer or would clearly get wrong — for example, "No documented ransom-payment policy; pay/no-pay decision unclear between CEO and board."
- Named owners for fixes. Each gap has one owner, one deliverable, one date. No anonymous "IT will look into it" entries.
The AlertMedia ransomware tabletop guide and the Cyber Management Alliance guide to 2026 tabletops both converge on this format.
Advertisement
Adapting the Exercise for Algerian Realities
Three local adjustments matter.
- Regulatory touchpoints. Substitute Algerian institutions into the inject script: the Banque d'Algérie for a financial incident, ARPCE for a telecom or data-sharing issue, the national CERT (DZ-CERT) for technical escalation, the ANPDP for personal data implications under the Algerian data-protection framework. Participants need to know whose phone number to dial, not just "call the regulator."
- Language. Run the exercise in the language of the leadership team — often a mix of Algerian dialect, French, and occasional MSA. A bilingual facilitator is more important than a written-English script.
- Three-sector consideration. Algerian leadership teams often include the ministry liaison or public shareholder representative. Include them. Crisis decisions around payment, disclosure, and media response are almost never purely private decisions in Algeria's institutional context.
What to Do After the First Tabletop
Organizations that run their first tabletop almost always conclude the same three things: backups are not as recoverable as assumed, the pay/no-pay decision has no written policy, and communications does not have a draft holding statement on file. Those three fixes, done properly, measurably improve incident outcomes.
Run a second tabletop six months later with a different scenario — a third-party SaaS breach, a destructive wiper, or a supply-chain compromise like a Shai-Hulud-type npm worm. The second exercise reveals whether the fixes from the first one stuck.
Where This Leaves Algerian CISOs
A DFIR tabletop exercise is the cheapest, highest-leverage readiness investment an Algerian organization can make in 2026. The templates are free. The facilitator can be internal. The participants are already on the org chart. Running one a year is the bar that regulators, insurers, and boards increasingly expect, and the first run will surface more useful fixes than any six-figure consulting engagement. The harder part is getting the CEO's calendar; everything after that is execution.
Frequently Asked Questions
Do we need external consultants to run a credible tabletop?
Not for the first one. A senior internal facilitator — typically the CISO or head of IT risk — using free templates from CISA's Tabletop Exercise Packages or the UK NCSC's Exercise in a Box can run an effective first exercise. External consultants add value later: for cross-sector scenarios, technical injects involving forensic decisions, or when the board wants independent validation.
How does this fit with Decree 26-07 cybersecurity units?
Every cybersecurity unit mandated by Decree 26-07 should run at least one tabletop per year as a basic maturity test. The decree itself does not specify the exercise, but regulators will increasingly look for evidence that leadership teams — not just IT — have practiced incident response. A dated after-action report is the simplest form of that evidence.
What if our leadership refuses to participate?
That itself is the finding. A tabletop that the CEO does not attend tells you your incident response program has a governance gap before the exercise even starts. The practical path is to frame the first tabletop as a board-level assurance request (insurers and auditors now ask for it), book 90 minutes with firm time-boxes, and make attendance visible. The exercise becomes easier to repeat once leadership sees the concrete gaps the first one surfaced.
Sources & Further Reading
- CISA Tabletop Exercise Packages
- UK NCSC Exercise in a Box — Tabletop Exercises
- Counter Ransomware Initiative Tabletop After-Action Report — Institute for Security and Technology
- How to Run a Ransomware Tabletop Exercise — AlertMedia
- The Ultimate Guide to a Cyber Tabletop Exercise in 2026 — Cyber Management Alliance
- Weekly Ransomware Trends April 2026: Qilin & DragonForce — Ransom-DB
- Algeria Orders Cybersecurity Units in Public Sector — Ecofin Agency
- Shai-Hulud 2.0: Guidance for Detecting, Investigating, and Defending — Microsoft Security Blog