When Vendor Risk Stopped Being a Category and Started Being the Norm
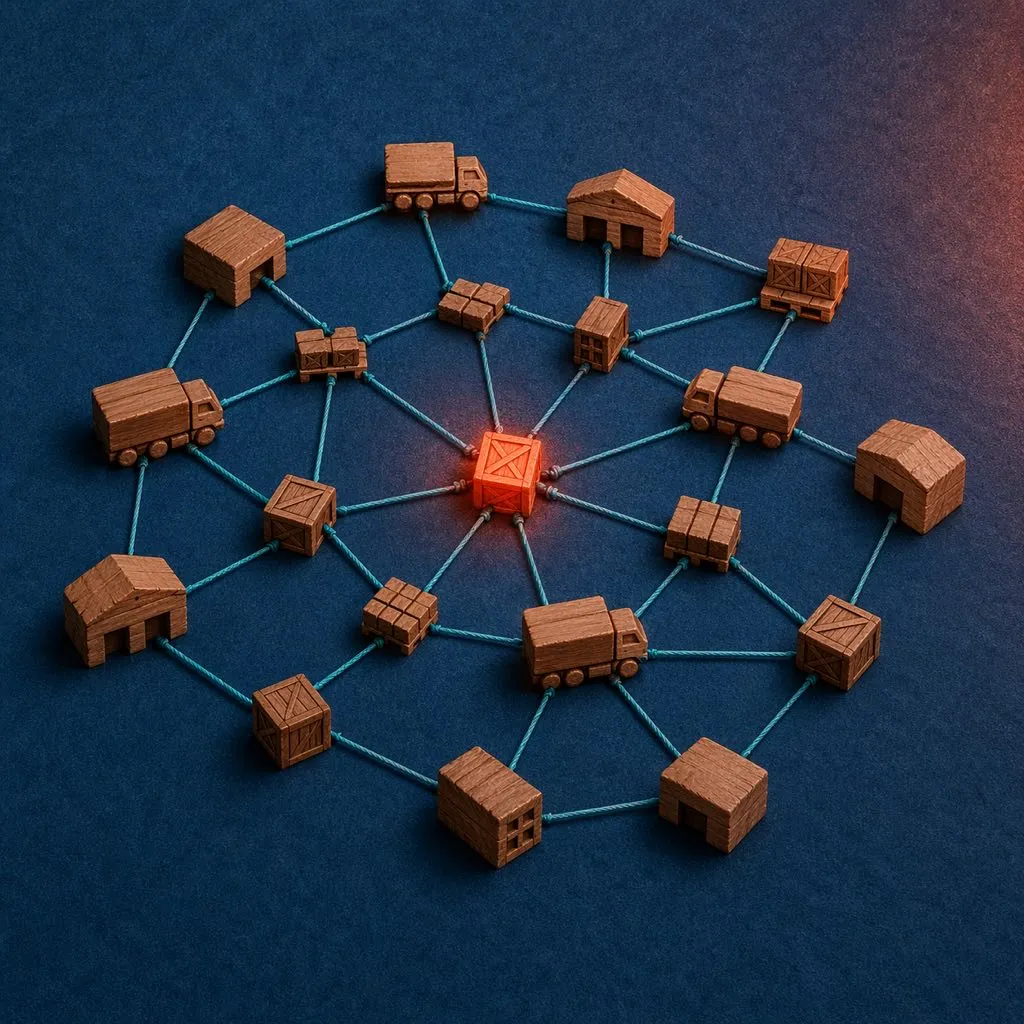
For a decade, “third-party risk management” was a compliance box adjacent to core cybersecurity — something for the GRC team, the vendor questionnaires, the annual SOC 2 review. The 2026 incident data has made that framing obsolete. Two major reports published in Q1 2026 converge on the same uncomfortable conclusion: supply chain compromise is no longer an emerging attack category. It is the default one.
Palo Alto Networks’ Unit 42 2026 Global Incident Response Report (February 17, 2026), based on more than 750 major incidents across over 50 countries, found that 23% of incidents involved attackers leveraging third-party SaaS applications for lateral movement or initial access. Bastion’s 2026 Supply Chain Security Report found that 70% of organizations experienced at least one third-party or software supply chain security incident in the past year, with 35.5% of breaches linked to third-party access and 41.4% of ransomware attacks involving third-party vectors.
The numbers converge because the underlying dynamic is the same: the enterprise attack surface has moved from hardened perimeters to sprawling SaaS and vendor ecosystems that no single organization controls end-to-end.
The Visibility Gap That Makes Everything Worse
The single most alarming number in Bastion’s report is not an attack statistic — it is a visibility statistic. Only 15% of CISOs say they have full supply chain visibility. Eighty-five percent of security leaders cannot fully enumerate the third-party software, SaaS integrations, OAuth grants, and vendor access paths that cross their own perimeter.
This is not a tooling gap; it is a governance gap. Most organizations know their top 20 strategic vendors in detail. The long tail — the AI productivity tool an engineer authorized into Google Workspace, the analytics widget a marketer installed on the customer portal, the open-source dependency the CI/CD pipeline pulls weekly — is unmapped. It is precisely in that long tail where 2026’s most significant breaches originated.
Consider the pattern in the last 18 months: the Salesloft/Drift OAuth cascade (ShinyHunters, 2026) pulled 1.5 billion Salesforce records from 760 companies via one stolen GitHub token. The Vercel/Context.ai breach (ShinyHunters, April 2026) compromised an entire platform through one employee’s OAuth grant to a third-party AI tool. The Shai-Hulud 2.0 npm worm (late 2025) affected 25,000+ GitHub repositories. None of these required breaking a hardened enterprise perimeter. All three exploited the trust relationships organizations extend to their vendors, integrations, and dependencies.
Advertisement
The Economic Cost Is Now Calibrated
Supply chain breaches are no longer a rhetorical risk — they carry calibrated financial impact. Bastion’s report cites $60 billion in global losses from supply chain attacks in 2025 and notes that a US breach with supply chain involvement costs on average $10.22 million. The Jaguar Land Rover incident in 2024, where attackers exploited a third-party SAP vulnerability, is estimated to have cost £1.9 billion in losses and affected over 5,000 supply chain organizations downstream.
IBM’s 2025 Cost of a Data Breach study found that breaches involving third-party compromises take an average of 267 days to identify and contain — nearly nine months during which attackers have ongoing access. And a 2026 analysis by Cyber Lab found that third-party involvement now accounts for approximately 30% of all data breaches, roughly double the rate from just a few years earlier.
For CFOs and boards, the rate-of-change is the number that matters. A vendor risk program calibrated to 2022 threat data is sized for a problem that has doubled in frequency and roughly tripled in attack tempo.
What “Default Vector” Means for Security Programs
When supply chain compromise is the default breach vector, three implications follow for security programs:
Vendor onboarding is no longer a one-time event. A SOC 2 report from vendor onboarding is a snapshot from the past. The 2026 breach landscape requires continuous monitoring of vendor security posture, including external attack surface data, leaked credential monitoring, and near-real-time vulnerability disclosure tracking for the vendor itself. Panorays, ReversingLabs, and others now offer continuous vendor monitoring platforms explicitly built for this cadence.
OAuth and SaaS integrations require the same governance as vendors. An OAuth grant to a third-party app is functionally equivalent to signing a data processing agreement with that vendor — except no one reviewed it. Every organization needs an authoritative OAuth inventory, periodic consent review, and allowlisting controls at the identity platform level.
Software Bills of Materials (SBOMs) must be operational, not archival. Most organizations that adopted SBOMs treat them as compliance artifacts. The operational use — pulling in vulnerability feeds, matching them to in-use components, triggering update workflows — is what prevents the next Log4Shell or XZ Utils event from becoming a breach rather than a near-miss. ReversingLabs’ 2026 report tracks 73% growth in open-source malware, much of it in packages pulled as transitive dependencies into production systems.
Detection content must cover the “through-the-trusted-path” scenario. Classic detection rules assume attackers come from outside. Supply chain attacks arrive inside trusted pipelines — a vendor API call, a signed software update, an OAuth-authorized sync. Detection content has to model these trusted paths as attack surface and flag anomalies within them.
A 2026 Checklist for Boards and CISOs
For organizations reviewing their third-party risk program in 2026, five items belong on the near-term agenda:
- Build a complete inventory of third parties, including SaaS integrations, OAuth grants, and software dependencies — not just the named vendors in procurement records.
- Measure current supply chain visibility against the 15% CISO benchmark — if inventory is incomplete, no downstream control works.
- Establish continuous monitoring for the top tier of vendors and all integrations with access to sensitive data.
- Operationalize SBOM ingestion with automated matching to vulnerability feeds and patch workflows.
- Run at least one tabletop exercise per year that starts with a trusted-vendor compromise scenario, not a perimeter breach scenario.
The 23% number from Unit 42 and the 70% number from Bastion are not ceilings — they are current-state measurements. Organizations that treat them as the new baseline will build programs that match the 2026 threat environment. Organizations that treat them as outliers will discover in their own incident reports why they weren’t.
Frequently Asked Questions
What is the difference between “supply chain” and “third-party risk” in the 2026 reports?
The two terms overlap but emphasize different angles. “Third-party risk” traditionally refers to vendors and service providers — the legal and contractual relationships an organization enters. “Supply chain” in the cybersecurity context extends to software components (open-source libraries, commercial software, build pipelines), SaaS integrations, OAuth apps, and any trusted data or code path that crosses the organization’s perimeter. Unit 42’s 23% statistic specifically refers to third-party SaaS applications; Bastion’s 70% figure includes the broader software supply chain.
How is this different from the 2020 SolarWinds era?
SolarWinds was a watershed, but it was primarily a compromise of a commercial software update pipeline. The 2026 landscape includes that attack pattern plus OAuth-based SaaS cascades (Salesloft/Drift, Vercel/Context.ai), open-source package compromise (Shai-Hulud 2.0, XZ Utils), and third-party ICS vendor exploitation (Jaguar Land Rover). The attack surface has broadened from software supply chain to trust-relationship supply chain, and the incident volume has roughly doubled.
What is the single highest-leverage action for a mid-sized organization?
Build a complete inventory of OAuth grants, SaaS integrations, and third-party software dependencies. Organizations cannot protect what they cannot enumerate, and Bastion’s data shows that only 15% of CISOs have full supply chain visibility. Before investing in continuous monitoring tools or SBOM platforms, ensure the inventory itself is complete and current — otherwise the downstream controls will have blind spots that match where breaches actually originate.