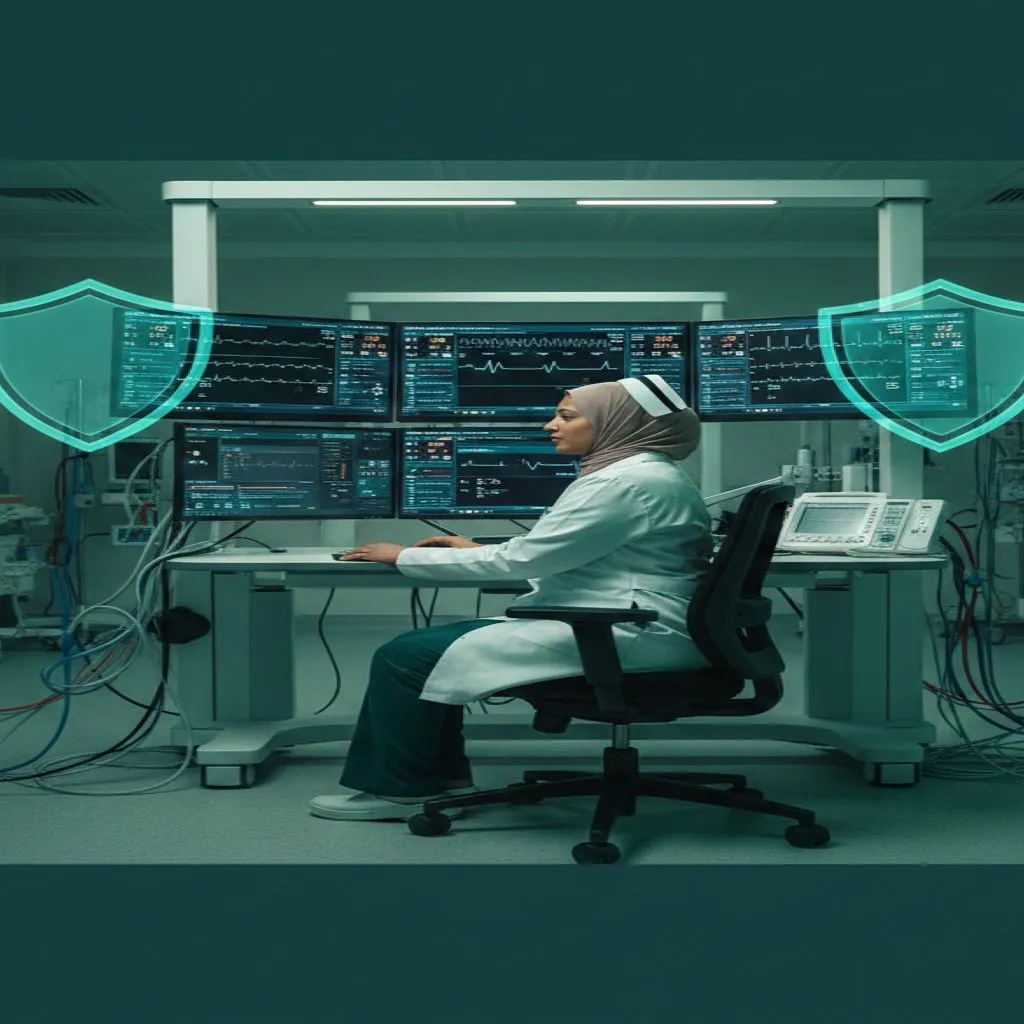
Healthcare Digitization Without Security
Algeria’s healthcare system is undergoing a digital transformation that was unthinkable a decade ago. University hospital centers (CHUs) in Algiers, Oran, Constantine, and Annaba have implemented electronic health record (EHR) systems, computerized physician order entry, and digital medical imaging (PACS). The Ministry of Health has launched multiple digital projects aimed at modernizing the health sector, while the CNAS (Caisse Nationale des Assurances Sociales) processes millions of claims electronically, linking pharmacies, hospitals, and clinics through a national reimbursement network. The Chifa card system, used by over 30 million beneficiaries, digitizes patient identification and insurance verification at the point of care. The recent rollout of the second-generation e-Chifa card — featuring enhanced chip technology with expanded data storage and an increased prescription reimbursement ceiling of 5,000 DZD per prescription — signals an acceleration of this digital trajectory.
Yet this digitization is proceeding with minimal cybersecurity planning. Globally, healthcare is the most targeted sector for cyberattacks, accounting for 22% of disclosed ransomware attacks in 2025 — a 30% surge from the previous year. IBM’s 2025 Cost of a Data Breach Report found that healthcare breaches cost an average of $7.42 million per incident, the highest of any industry for the 15th consecutive year. The Verizon 2025 Data Breach Investigations Report recorded 1,710 security incidents in healthcare, with 1,542 confirmed data disclosures. The Health-ISAC 2026 report has described the situation as an “existential cybersecurity crisis” for the sector.
Healthcare is attractive to attackers for structural reasons: organizations cannot afford downtime because patients’ lives depend on system availability, they hold highly sensitive personal data (medical records sell for up to $1,000 each on dark web markets — roughly 10 times the value of credit card numbers), and their IT systems often run legacy software with known vulnerabilities.
Algeria is not exempt from this global threat landscape. The combination of newly connected systems, limited IT security staffing, and the absence of healthcare-specific cybersecurity regulations creates a risk environment that deserves urgent attention before a major incident occurs, not after.
The Attack Surface: Connected Systems in Algerian Hospitals
A typical CHU in Algeria now operates with several interconnected digital systems. Hospital Information Systems (HIS) manage patient admissions, discharge, and transfers. PACS (Picture Archiving and Communication Systems) store and distribute medical imaging — X-rays, CT scans, MRIs — in DICOM format across the hospital network. Laboratory Information Systems (LIS) manage blood tests and pathology results. Pharmacy management systems track medication inventory and dispensing. Each of these systems processes, stores, or transmits protected health information.
The security challenge is compounded by medical devices. Modern infusion pumps, patient monitors, ventilators, and imaging equipment run embedded operating systems (often Windows XP Embedded or Linux variants) that connect to hospital networks for data exchange. These devices are rarely patched — manufacturers control software updates, update cycles are slow, and taking a medical device offline for patching in a busy ICU is operationally difficult. The 2017 WannaCry ransomware attack devastated the UK’s National Health Service precisely because it exploited unpatched Windows systems in hospitals, including diagnostic imaging equipment. More than 60 NHS trusts were affected, with costs estimated at 92 million GBP.
In Algerian hospitals, the network segmentation that should isolate medical devices from administrative systems and internet-facing servers is often absent or poorly implemented. A flat network architecture means that malware entering through a phishing email on an administrative workstation can propagate to clinical systems handling patient data. Site visits to Algerian healthcare facilities reveal common vulnerabilities: shared passwords for system access, USB drives used freely between personal and hospital computers, and wireless networks without enterprise-grade authentication.
Advertisement
Patient Data Protection: From Law 18-07 to Law 25-11
Algeria’s data protection framework has evolved significantly in recent years, though healthcare-specific cybersecurity rules remain absent. The foundational legislation, Law 18-07 (June 2018) on the protection of natural persons with regard to the processing of personal data, established general principles for data processing: lawfulness, purpose limitation, data minimization, accuracy, and security. The law designated health data as “sensitive data” requiring enhanced protection, including explicit consent for processing and special authorization from the ANPDP (Autorite Nationale de Protection des Donnees a caractere Personnel). However, Law 18-07 only became fully applicable in August 2023, after the ANPDP was installed in August 2022 and began operations — a five-year implementation delay that left the framework dormant during a critical period of healthcare digitization.
A major regulatory development came with Law 25-11 (July 2025), which amended Law 18-07 and introduced several provisions directly relevant to healthcare cybersecurity. Most notably, Law 25-11 mandates breach notification to the ANPDP within 5 days of discovery — closing what had been one of the most critical gaps in Algeria’s data protection regime. The amendment also requires the mandatory appointment of Data Protection Officers (DPOs), Data Protection Impact Assessments (DPIAs), and detailed processing records. These obligations apply to healthcare entities handling sensitive patient data.
Algeria’s cybersecurity posture has been further reinforced at the national level. Presidential Decree 25-321 (December 2025) approved the National Cybersecurity Strategy 2025-2029, and Presidential Decree 26-07 (January 2026) established dedicated cybersecurity units within public institutions — a measure that directly applies to public hospitals and CHUs.
However, these remain general-purpose frameworks. Law 18-07, even as amended by Law 25-11, does not contain healthcare-specific cybersecurity requirements equivalent to the US HIPAA Security Rule, which mandates specific technical safeguards (encryption standards, access controls, audit logging, emergency access procedures) and administrative safeguards (risk assessments, workforce training, incident response plans) for any entity handling protected health information. HIPAA also requires breach notification within 60 days and imposes penalties reaching up to $2.19 million per violation for the most severe tier of willful neglect. While Algeria’s 5-day notification window is actually stricter than HIPAA’s 60-day timeline on paper, the enforcement infrastructure and healthcare-specific technical standards are not yet in place.
A sectoral health data security regulation — mandating encryption, access controls, audit trails, and incident reporting specifically for all healthcare entities processing patient data — remains the most important regulatory gap to close. The WHO published its cybersecurity and privacy maturity assessment guide for digital health information systems in March 2025, offering a ready-made framework that Algeria’s Ministry of Health could adapt.
Building Healthcare Cyber Resilience
The path forward requires action at institutional, regulatory, and national levels. At the hospital level, CHU directors and IT managers should conduct formal cybersecurity risk assessments of all connected systems, prioritizing those handling patient data. Network segmentation — separating medical devices, clinical workstations, administrative systems, and guest WiFi into isolated network zones with controlled access between them — is the single most impactful technical measure and can be implemented with existing switch and firewall infrastructure.
Mandatory cybersecurity training for healthcare workers is equally critical. Phishing remains the primary attack vector in healthcare breaches globally, and clinical staff who are trained to identify suspicious emails and links represent the strongest first line of defense. Training programs should be continuous, not one-time, and tailored to healthcare workflows — for example, teaching staff to verify emailed “lab results” or “patient referrals” before opening attachments.
At the national level, Algeria’s Ministry of Health should develop a healthcare cybersecurity framework with input from the ANPDP, CERIST, and international organizations like the WHO (which published its cybersecurity maturity assessment guide for digital health systems in March 2025) and the International Telecommunication Union. This framework should mandate minimum security standards for healthcare IT systems, require regular security audits for CHUs and major healthcare facilities, establish a healthcare-specific CERT (Computer Emergency Response Team) or sector coordination center, and create a confidential incident reporting mechanism that encourages disclosure without penalty. The new cybersecurity units mandated by Presidential Decree 26-07 provide a structural foundation, but they need healthcare-specific guidance to be effective in clinical environments. The cost of inaction is not theoretical — it is measured in patient safety, data privacy, and the public’s willingness to trust digital healthcare.
Frequently Asked Questions
What is cybersecurity in algerian healthcare?
Cybersecurity in Algerian Healthcare: Hospital Systems, Patient Data covers the essential aspects of this topic, examining current trends, key players, and practical implications for professionals and organizations in 2026.
Why is cybersecurity in algerian healthcare important for Algeria?
This topic is significant for Algeria because it intersects with the country’s digital transformation goals, economic diversification strategy, and growing technology ecosystem. The article provides specific context for Algerian stakeholders.
How does the attack surface: connected systems in algerian hospitals work?
The article examines this through the lens of the attack surface: connected systems in algerian hospitals, providing detailed analysis of the mechanisms, trade-offs, and practical implications for stakeholders.
Sources & Further Reading
- IBM Cost of a Data Breach Report 2025 — IBM Security
- Healthcare Data Breach Costs 2025 — HIPAA Journal
- Healthcare Most Targeted Sector for Ransomware 2025 — HIPAA Journal
- Algeria Data Protection Law 18-07 and Amendments (Law 25-11) — CMS Law
- Algeria Digital Policy Updates — Digital Policy Alert
- HIPAA Violation Fines and Penalties 2026 — HIPAA Journal
- Chifa Card and Third Party Payment System — CNAS Algeria
- e-Chifa Card Launch and Reimbursement Update — APS
- WHO Cybersecurity Guide for Digital Health Systems
- WannaCry Cyber Attack Impact on NHS — National Health Executive