 ALGERIATECH Editorial
ALGERIATECH Editorial

Policy & Regulation
Digital Trade Agreements: The Invisible Rules Shaping How Data and Services Cross Borders
The Quiet Architecture of the Digital Economy The rules governing how data crosses borders are not being written by technologists or privacy advocates. They are being written by trade negotiators, embedded in agreements that most people never read, and they will determine

Policy & Regulation
The Taxation of Digital Giants: Digital Services Taxes, OECD Pillar One, and the $200 Billion Question
The Problem: Where Value Is Created vs. Where Profits Are Booked The international corporate tax system was designed in the 1920s for an economy of factories, mines, and shipping routes.

Cybersecurity & Risk
Digital Forensics and Incident Response: Inside the Teams That Investigate Cyberattacks
When the Breach Alarm Sounds The moment an organization confirms it has been breached — ransomware encrypting production servers, a threat actor detected in the network, customer data appearing on a dark web forum — a clock starts. The first 48 hours are critical.

Infrastructure & Cloud
The Data Lakehouse Revolution: How Apache Iceberg and Delta Lake Are Reshaping Data Architecture
The Architecture That Ate Both Worlds For two decades, enterprise data lived in one of two places. Structured data — transactions, customer records, financial reports — went into data warehouses: Teradata, Oracle, and later Snowflake and BigQuery.

Skills & Careers
Data Engineering: The Most In-Demand Infrastructure Role Nobody Talks About
The Role Behind the AI Revolution Every headline about AI mentions models, algorithms, and billion-parameter architectures. Almost none mention the infrastructure that makes AI work: the data pipelines that collect, clean, transform, and deliver the terabytes of training and

Skills & Careers
Developer Relations in 2026: The Career That Bridges Code, Community, and Business
From Tech Evangelism to Strategic Growth Function Developer Relations has undergone a fundamental transformation over the past decade. What began as "tech evangelism" -- charismatic engineers giving conference talks and handing out stickers -- has evolved into a strategic

Cybersecurity & Risk
Cybersecurity in Space: Satellite Hacking, GPS Spoofing, and the Vulnerability of Orbital Infrastructure
The Viasat Wake-Up Call On February 24, 2022 -- exactly four years ago today -- as Russian forces began their invasion of Ukraine, a sophisticated cyberattack disabled Viasat's KA-SAT satellite broadband network across Europe. The attackers exploited a misconfigured VPN

Infrastructure & Cloud
The Developer Platform Revolution: How Vercel, Netlify, Railway, and Render Are Redefining Cloud for Builders
The Rise of DX-First Cloud Platforms A fundamental shift is underway in how developers interact with cloud infrastructure. For the past 15 years, AWS, Azure, and Google Cloud dominated the conversation with an ever-expanding catalog of services — hundreds of products,

Cybersecurity & Risk
CSPM and CNAPP: Why Cloud Security Is the Biggest Line Item in Cybersecurity Budgets
The Misconfiguration Epidemic: Cloud's Biggest Threat Is Not Hackers Here is an uncomfortable truth that the cybersecurity industry has spent years dancing around: the majority of cloud breaches are not caused by sophisticated hackers exploiting zero-day vulnerabilities. They

Infrastructure & Cloud
The Great Cloud Repatriation: Why Some Companies Are Bringing Workloads Back On-Premise
The Cloud-First Era Meets Its Counterargument For the better part of a decade, the technology industry operated under a simple orthodoxy: move everything to the cloud. In 2019, Gartner predicted that 80% of enterprises would shut down their traditional data centers by 2025.
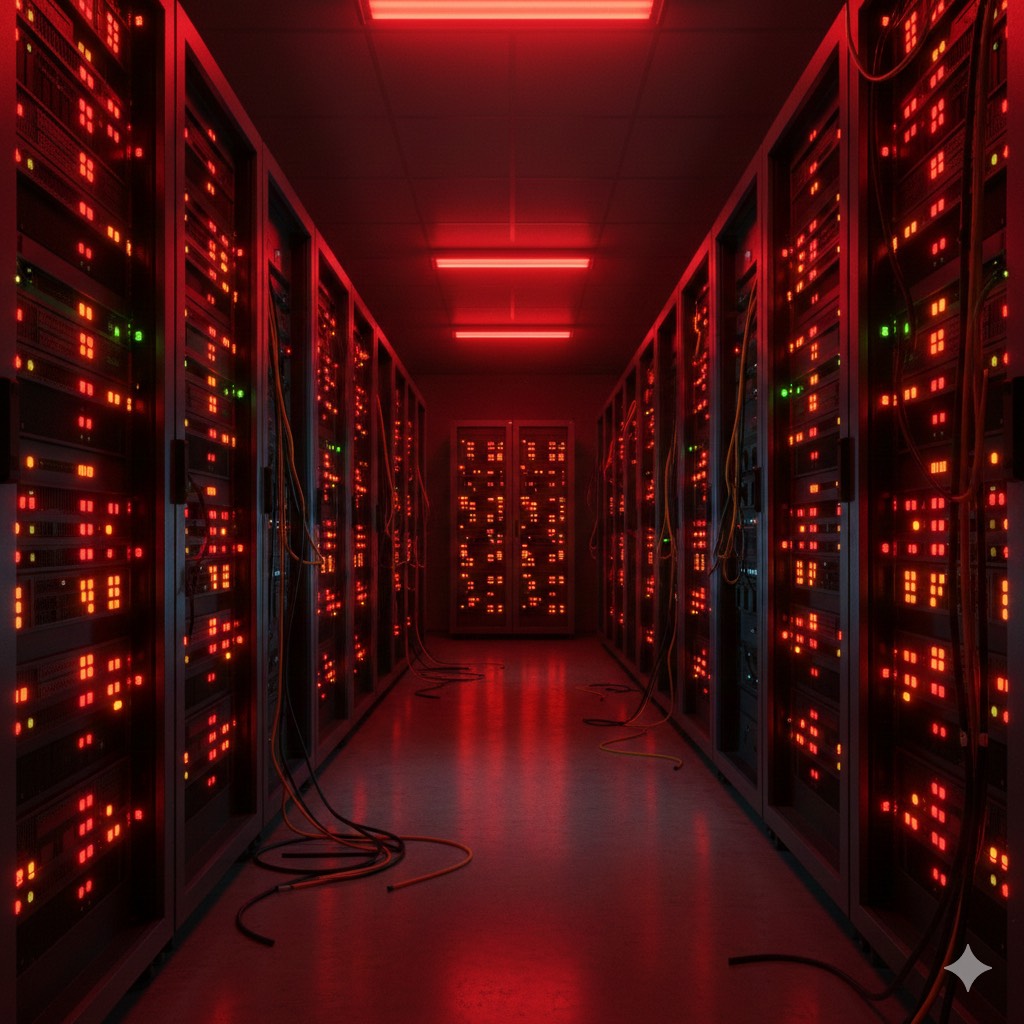
Infrastructure & Cloud
When the Cloud Goes Down: The State of Disaster Recovery and Business Continuity in 2026
The Illusion of Five Nines The cloud computing industry sells availability. AWS promises 99.99% uptime for most services.





