The Quiet Announcement That Reframes Cloud Strategy
For more than a decade, “multi-cloud” has been an analyst buzzword that collided with an uncomfortable reality: connecting AWS, Google Cloud and Azure at production scale was a networking archaeology project. Private peering across providers required specialized colocation facilities, custom BGP configurations, and operations teams that could read three different sets of documentation without mixing them up. The friction kept most enterprises effectively single-cloud, even when they bought from multiple vendors.
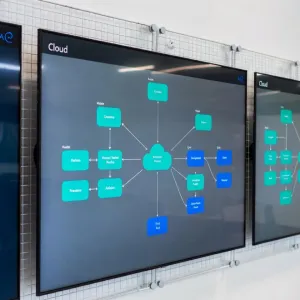
That is now changing. In April 2026, AWS announced general availability of AWS Interconnect – multicloud, a managed service that lets customers provision private, high-bandwidth, resilient connections between their Amazon VPCs and other public clouds “in a few clicks.” Google Cloud is the launch partner. Microsoft Azure and Oracle Cloud Infrastructure are confirmed to join later in 2026, using the same open specification.
When the third major hyperscaler ships the same API surface, a single networking architecture suddenly covers every combination — AWS-to-GCP, AWS-to-Azure, GCP-to-Azure, or all three. The biggest technical objection to multi-cloud is being removed by the very providers who benefited from its absence.
What AWS Interconnect-Multicloud Actually Does
The service is simple to describe and materially different from what existed before. Customers provision a managed cross-cloud circuit with:
- Dedicated private bandwidth, not internet transit
- Encrypted physical links between AWS routers and the partner CSP’s routers
- 4-way resiliency built in — multiple physical paths with automatic failover
- Few-click provisioning through each cloud’s native console, instead of managing colocation circuits manually
- An open interoperability specification that any cloud provider can implement
Google Cloud’s parallel offering — Cross-Cloud Interconnect, extended to AWS and then to additional partners — uses the same open specification. This is the detail that matters most. It means the three hyperscalers are not each building proprietary bridges to each other. They are standardizing on a shared interoperability layer that third parties can also implement.
Why All Three Players Gave In at Once
Cloud providers historically resisted easy interconnect because egress revenue and lock-in were powerful moats. Three forces forced the change:
- Customer pressure. According to Flexera’s 2026 State of the Cloud Report, 94% of enterprises now use cloud services and 87% have a multi-cloud strategy. Further surveys report 84% of cloud leaders intentionally opt for multiple clouds. Ignoring that demand was no longer sustainable.
- AI workload diversity. Large enterprises running AI pipelines now need compute from more than one provider — Trainium on AWS, TPUs on Google, MI300X on Azure via NDv5, NVIDIA H200 wherever it is available. Moving data between those compute pools cheaply is a precondition for real multi-vendor AI.
- Regulatory pressure. The EU’s Digital Operational Resilience Act (DORA), UK PRA guidance on concentration risk, and similar frameworks in Australia, Japan and Singapore explicitly require regulated enterprises to demonstrate cloud exit and multi-cloud resilience plans. Single-cloud deployments in financial services are increasingly non-compliant.
Forrester’s 2026 Warning: Two Major Cloud Outages This Year
The timing of the interconnect launch is not coincidental. Forrester’s Predictions 2026 report warns that at least two major multi-day cloud outages will occur in 2026. The reasoning: hyperscalers are diverting investment away from legacy x86 and ARM environments, prioritizing GPU-centric AI data centers while aging control planes and networking layers accumulate technical debt.
The 2025 AWS us-east-1 outage and the large Azure disruption in the same year were the warning shots. Forrester’s analysis is that those outages will force enterprises to rethink cloud strategy “not just for resilience but for control, especially for their big bets on AI.” That translates into the forecast that at least 15% of enterprises will shift toward private AI deployments on private clouds in 2026, and a further reallocation toward neoclouds — CoreWeave, Lambda, Nebius and others — which are projected to capture $20 billion in revenue in 2026 alone.
Against that backdrop, easy multi-cloud interconnect is not a nice-to-have feature. It is the architectural primitive that makes realistic cloud resilience possible.
Advertisement
What This Unlocks for Enterprises
Disaster recovery that actually works. Previously, declaring a secondary cloud as your DR target meant duplicating data synchronization infrastructure and absorbing brutal egress costs during failover. With managed interconnect, cross-cloud replication becomes a routine operational task rather than a project.
Workload-level vendor optimization. Running inference on Trainium at AWS, training on TPUs at Google, and hosting customer-facing applications on Azure is now feasible as a single logical architecture. The same customer data can transit between them securely and cheaply enough to matter.
Negotiating leverage. Enterprises that can credibly move workloads between clouds can demand better pricing. The interconnect removes the single biggest technical argument against threatening to switch.
Regulatory compliance. DORA, PRA, and equivalent regimes become easier to satisfy. Auditors want to see operational cloud exit plans, not architecture diagrams that quietly depend on a single provider.
What It Does Not Solve
Multi-cloud remains hard for reasons that have nothing to do with networking:
- Identity and access. IAM is still fragmented across providers; federated identity requires careful design.
- Data gravity. Storage services are not portable. Moving petabytes takes time and money, regardless of bandwidth.
- Operational complexity. Two or three clouds mean two or three sets of monitoring, logging, incident response, and cost tooling.
- Talent. Teams fluent in one cloud are rare. Teams fluent in three are rarer and expensive.
These remain real costs. But they are now the only costs, because the one technical wall that used to make multi-cloud economically infeasible — affordable, production-grade cross-cloud networking — has been dismantled.
Enterprise Implications
- Revisit resilience plans. If your last cloud resilience assessment assumed cross-cloud connectivity was too hard, the assumption is no longer valid. Board risk committees should be asking for updated designs.
- Prepare for Azure GA. Once Azure joins later in 2026, three-way architectures become practical. Start design work now so you are ready when the GA lands.
- Renegotiate committed-use contracts. Multi-cloud credibility improves your hand on any large 2026-2027 commitment.
- Watch the neoclouds. Forrester’s forecast implies a real shift of AI workloads toward CoreWeave, Lambda and Nebius. The interconnect specification is open, which means neoclouds can implement it too and offer compatible connectivity without the hyperscalers as gatekeepers.
What to Watch Next
- Azure Interconnect GA date — the moment the three-cloud architecture is fully available.
- Oracle Cloud Infrastructure join — promised for later 2026.
- Interconnect specification adoption by neoclouds — CoreWeave and Lambda would change the competitive balance if they ship it.
- First major 2026 cloud outage — Forrester’s forecast will either be confirmed or quietly revised.
Multi-cloud spent a decade as a buzzword. 2026 is the year it becomes an architecture. For enterprises that have been waiting for the technical barriers to come down, the wait is over.
Frequently Asked Questions
How is AWS Interconnect-multicloud different from private peering or a VPN?
It is a managed service rather than a networking project. Previously, connecting AWS to Google Cloud or Azure at production scale required colocation space, custom BGP configurations, and manual resilience design. Interconnect-multicloud provisions dedicated private bandwidth with encrypted links and 4-way resiliency in a few clicks from the native cloud console, using an open interoperability specification that any cloud provider can implement.
Do I need multi-cloud if I have never had an outage?
Regulatory frameworks like DORA, UK PRA concentration-risk guidance, and equivalent regimes in Australia, Japan and Singapore increasingly require regulated enterprises to demonstrate cloud exit and multi-cloud resilience plans. Forrester is also forecasting at least two major multi-day cloud outages in 2026. Even without a personal outage history, the combined regulatory and reliability pressure makes cross-cloud failover a strategic requirement for financial services, healthcare, and critical-infrastructure operators.
What problems does multi-cloud still not solve?
Identity and access management remains fragmented across providers. Storage services are not portable, so moving petabytes of data takes time and money regardless of bandwidth. Operational complexity doubles or triples — two or three sets of monitoring, logging, incident response, and cost tooling. And skilled staff fluent across multiple clouds are rare and expensive. Interconnect removes the networking wall but not the operational and talent costs.
Sources & Further Reading
- AWS announces general availability of AWS Interconnect – multicloud — AWS
- AWS and Google Cloud collaborate on multicloud networking — Google Cloud Blog
- Azure follows Google in joining AWS multicloud initiative — Intercept
- Predictions 2026: Cloud Outages, Private AI, and the Rise of the Neoclouds — Forrester
- Forrester Predicts Two Major Cloud Outages in 2026 — OpenMetal